In this article, I’m going to show you the way of configuring audit policy on Windows server 2016. As in our previous topics, we have told you how to configure lockout policy and as well as configuring password policy on Windows server 2016. Configuring audit policy can be applied to Microsoft Windows server 2003, Windows server 2008, server 2012 and Windows 10 operating system with its previous versions.
What is Audit Policy?
Whenever you configure audit policy in Windows server or any client. This policy will allow or help you to get information about who logged into your computer? When he or she logged in or from where that user logged in. And as well as give you information about any kinds of event that happen on that computer. By configuring audit policy, you can get all this information. To get known about these events, go to the event section then take all the info. Now, we’re going to explain the following policies.
#1. Audit Account Logon Events
This security setting determines whether the OS audits each time this computer validates an account’s credentials.
Account logon events are generated whenever a computer validates the credentials of an account for which it is authoritative. Domain members and non-domain-joined machines are authoritative for their local accounts; domain controllers are all authoritative for accounts in the domain. Credential validation may be in support of a local login, or, in the case of an Active Directory domain account on a domain controller, may be in support of a login to another computer. Credential validation is stateless so there is no corresponding logoff event for account login events.

Audit Account Logon Events
If this policy setting is defined, the administrator can specify whether to audit only successes, only failures, both successes and failures or to not audit these events at all.
#2. Audit Account Management
This security setting determines whether to audit each event of account management on a computer. Examples of account management events include:
- A user account or group is created, changed, or deleted.
- A user account is renamed, disabled, or enabled.
- A password is set or changed.
If you define this policy setting, you can specify whether to audit successes, audit failures or not audit the event type at all. Success audits generate an audit entry when any account management event succeeds. Failure audits generate an audit entry when any account management event fails. To set this value to No auditing, in the Properties dialog box for this policy setting, select the Define these policy settings check box and clear the Success and Failure check boxes.

Audit Account Management
#3. Audit Directory Service Access
This security setting determines whether the OS audits user attempts to access Active Directory objects. The audit is only generated for objects that have system access control lists (SACL) specified, and only if the type of access requested (such as Write, Read, or Modify) and the account making the request match the settings in the SACL.
The administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all (i.e. neither successes nor failures). If Success auditing is enabled, an audit entry is generated each time any account successfully accesses a Directory object that has a matching SACL specified.

Audit Directory Service Access
If Failure auditing is enabled, an audit entry is generated each time any user unsuccessfully attempts to access a Directory object that has a matching SACL specified.
#4. Audit Logon Events
This security setting determines whether the OS audits each instance of a user attempting to log on to or to log off to this computer. Logoff events are generated whenever a logged on user account’s login session is terminated. If this policy setting is defined, the administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all.
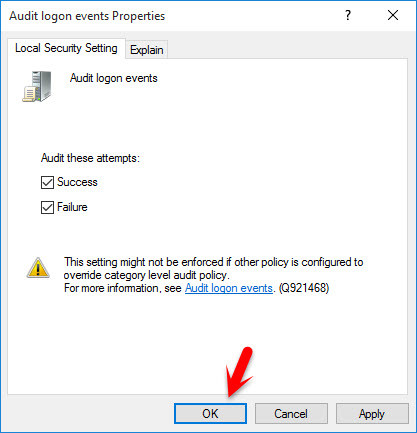
Audit Logon Events
#5. Audit Object Access
This security setting determines whether the OS audits user attempts to access non-Active Directory objects. The audit is only generated for objects that have system access control lists (SACL) specified, and only if the type of access requested (such as Write, Read, or Modify) and the account making the request match the settings in the SACL.
The administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all.
If Success auditing is enabled, an audit entry is generated each time any account successfully accesses a non-Directory object that has a matching SACL specified.

Audit Object Access
If Failure auditing is enabled, an audit entry is generated each time any user unsuccessfully attempts to access a non-Directory object that has a matching SACL specified. Note that you can set an SACL on a file system object using the Security tab in that object’s Properties dialog box.
#6. Audit Policy Change
This security setting determines whether the OS audits each instance of attempts to change user rights assignment policy, audit policy, account policy, or trust policy. The administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all (i.e. neither successes nor failures).
If Success auditing is enabled, an audit entry is generated when an attempted change to user rights assignment policy, audit policy, or trust policy is successful.

Audit Policy Change
If Failure auditing is enabled, an audit entry is generated when an attempted change to user rights assignment policy, audit policy, or trust policy is attempted by an account that is not authorized to make the requested policy change.
#7. Audit Privilege Use
This security setting determines whether to audit each instance of a user exercising a user right. If you define this policy setting, you can specify whether to audit successes, audit failures or not audit this type of event at all. Success audits generate an audit entry when the exercise of a user right succeeds. Failure audits generate an audit entry when the exercise of a user right fails.

Audit Privilege Use
To set this value to No auditing, in the Properties dialog box for this policy setting, select the Define these policy settings check box and clear the Success and Failure check boxes.
#8. Audit Process Tracking
This security setting determines whether the OS audits process-related events such as process creation, process termination, handle duplication, and indirect object access. If this policy setting is defined, the administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all.
Audit Process Tracking
If Success auditing is enabled, an audit entry is generated each time the OS performs one of these process-related activities. If Failure auditing is enabled, an audit entry is generated each time the OS fails to perform one of these activities.
#9. Audit System Events
This security setting determines whether the OS audits any of the following events:
- Attempted system time change
- Attempted security system startup or shutdown
- Attempt to load extensible authentication components
- Loss of audited events due to auditing system failure
- Security log size exceeding a configurable warning threshold level.
If this policy setting is defined, the administrator can specify whether to audit only successes, only failures, both successes and failures, or to not audit these events at all (i.e. neither successes nor failures).
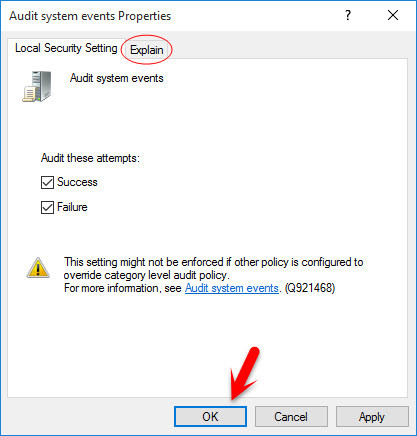
Audit System Events
If Success auditing is enabled, an audit entry is generated each time the OS performs one of these activities successfully. If Failure auditing is enabled, an audit entry is generated each time the OS attempts and fails to perform one of these activities.
Conclusion
These were all about how to configure Audit Policy in Windows Server 2016 or any other version of Windows servers. If you have got any question regarding this article, please feel free to ask your question below this post. Thanks for being with us.


Thank you for the explanation. It is better to explain regarding the check loged events following your article.